Items to watch out for when implementing GPO / RDP security policies on a Cameyo server
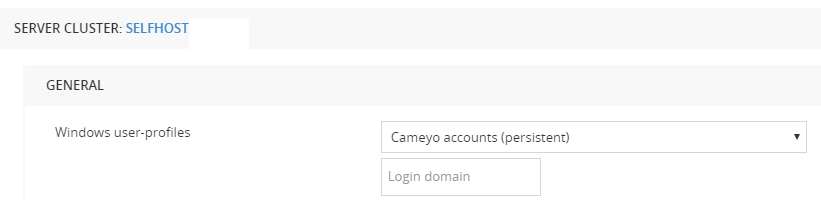
In most configuration scenarios, Cameyo manages its own Windows user profiles and accounts. Depending on the Cameyo's server configuration (online.cameyo.com/servers), a Cameyo user profile's lifecycle can either be temporary ("Temporary users"), in which case user accounts and profiles are created and suppressed upon session start / end, or it may live longer, assigning each physical Cameyo user to the same Windows profile ("Cameyo accounts").
Given the extreme complexity of Windows GPO settings it is difficult to establish an exact guideline for GPO do's and do not's, but here are some main high-level items to beware of:
- Remote users: Cameyo-managed user accounts must be part of the Remote Desktop Users usergroup. When generating users, Cameyo adds then to this usergroup. But it may be that your Active Directory / GPO policy overwrites it once in a while, thereby removing those users from this usergroup.
- Password enforcement rules: Cameyo-managed user accounts have their own password. Cameyo-managed passwords are extremely long and complex. Make sure your GPO policy does not impose a maximum password length or limitation, as Cameyo passwords typically grow beyond human password length or complexity.
- Internet filtering, connectivity and proxying: Cameyo's modules require access to the Cameyo portal. Sometimes corporate network policy restricts some computers or users to a predefined set of URLs, or requires going through a proxy. Make sure you exclude Cameyo's Web addresses: at least files.cameyo.com, online.cameyo.com on port 443.
For more information about troubleshooting RDP-level connectivity issues, see Diagnosing RDP connectivity issues.
Missing tsclient storage or contains strange files
If browser storage (download / upload) are not available and \\tsclient\storage is missing, watch out for the following line in c:\guacd\logs:
[14-09-2021 06: 30: 29: 384] [guacd] [PID: 981 = 0] [ERROR] Failed to perform interactive logon or get user profile directory. Drive will be disabled.
If you see this error in the log file, make sure you add the Users group to following GPO policy item (gpedit.msc):
Computer Configuration> Windows Settings > Security Settings> Local Policies> User Rights Assignment> Allow log on locally

- Goto Computer Configuration > Windows Settings > Security Settings> Local Policies> User Rights Assignment
- Select the policy Allow log on locally
- Check if the groups Users is there
if not, proceed to #4, otherwise this is not the problem - Click [Add User or Group]
- Click [Object Types]
- Select Groups (this is not selected by default)
- Enter Users
- Click OK
- Check Users is in the list
- Click OK
