Cameyo's proprietary Port Shield defends servers against cyber attacks by keeping RDP and HTTP ports closed at all times, except when needed.
You may not know it, but as soon as you enable Remote functionality on a Windows machine you effectively open its RDP ports to the outside world, specifically ports 3389, 3387, 3392. Hence, if your server is directly connected to the Internet, you are vulnerable to RDP brute-force and vulnerability attacks.
According to our own study, a Windows device directly connected to the Internet is prone to hundreds of thousands of password attempts every week, performed by automated bots, scripts, viruses and zombie machines. RDP exploits are also part of the equation, with vulnerabilities such as BlueKeep.
HTTP vulnerabilities are also discovered from time to time. And although critical HTTP server vulnerabilities are rare, Cameyo helps you reduce the surface of attack.
Cameyo's defense
Cameyo Port Shield is a dynamic protection which, when enabled, keeps your server's RDP and HTTP(S) ports closed at all times, opening them selectively for certain users, only when needed. It does so by managing the Windows Firewall. Initially, all ports are closed and are then selectively opened towards authenticated users when needed. It works by creating and managing real-time IP white-listing firewall rules for inbound RDP / HTTP ports on Cameyo servers.
Activation
The Port Shield functionality can be configured on your Cameyo's server page. It is enabled by default for cloud instances, and turned off by default for on-premise servers, although it is recommended in both scenarios.

You can add a list of ; semicolon-separated IP addresses that always need to be allowed through. In most cases this is not necessary, as even administrative access is dynamically allowed when needed, as explained below. Changing this setting requires a service restart. This can be done using the "Restart service" button.
Under the hood
Cameyo Port Shield works in 3 phases:
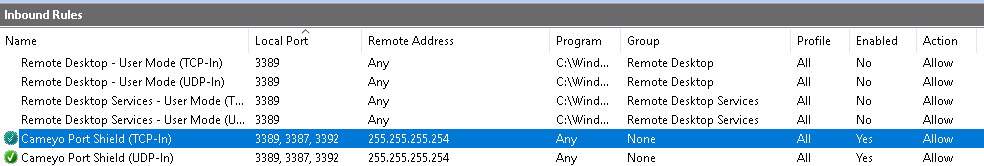
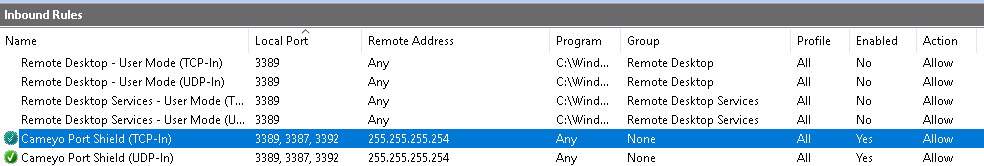
- Upon service start, Cameyo disables any existing Windows Firewall rules that allow access to RDP/HTTP ports. It then adds its own white-list rules named "Cameyo Port Shield (TCP/UDP-In)" for RDP ports and "Cameyo HTTP Port Shield (TCP/UDP-In)" for HTTP ports. Cameyo's portal as well as white-listed "admin IPs" addresses (if specified) are added as pre-authorized remote addresses; otherwise a placeholder address "255.255.255.254" is added instead. At this point, RDP/HTTP ports are closed for access.
- When authorized Cameyo sessions are initiated through the Cameyo portal (i.e. online.cameyo.com/apps/xxxxx/play), one of two scenarios take place:
- For regular HTML5 sessions, if HTTP Port Shield is enabled, Cameyo's portal informs the relevant server to open HTTP(S) access to the requesting user's IP address.
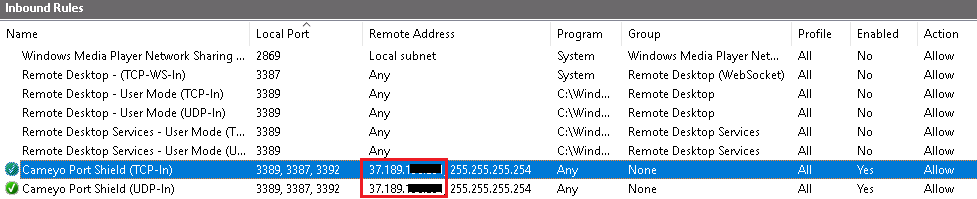
- When direct RDP sessions are started (through Cameyo's Native Player / Android app / administrator's "Generate .RDP file" function), Cameyo's portal informs the relevant server to open RDP port to the requesting user's IP address. Direct RDP sessions are only used for native Windows clients / Android app / explicit administrator RDP connection.
- White-listed IP addresses are removed and cleaned up upon Cameyo service start / restart, typically twice a day.

Example workflow
In the below example, Cameyo's Port Shield has disabled built-in RDP allow rules. It added its own rule with placeholder 255.255.255.254 address.
Following a portal-authenticated direct RDP session request, Port Shield has added authorization for the RDP connections coming from the 37.189.xxx.xxx address:
This access permission will be cleared up upon the next Cameyo service restart within a few hours, bring it back to pre-white-listed IP addresses only: